AirWatch recently released a iOS version 5.2 of Anirwatch Agent App.
Please see below for details of the app update:
Introducing VMware AirWatch® Agent 5.2 for iOS
The VMware AirWatch® team is excited to announce that AirWatch Agent 5.2 for iOS is publicly available.
What’s New in this App Version
• Implemented Apple’s App Transport Security (ATS) which enforces best practices in secure connections using TLS 1.2 with forward secrecy.
• Improved user experience for SSO
We have identified at least one server that does not seem to be complaint with the ATS standard causing an SSL error during enrollment.
Below is how Apple defines ATS( App Transport Security)
Starting in iOS 9.0 and OS X v10.11, a new security feature called App Transport Security (ATS) is available to apps and is enabled by default. It improves the privacy and data integrity of connections between an app and web services by enforcing additional security requirements for HTTP-based networking requests. Specifically, with ATS enabled, HTTP connections must use HTTPS (RFC 2818). Attempts to connect using insecure HTTP fail. Furthermore, HTTPS requests must use best practices for secure communications.
The NSAppTransportSecurity key is supported in iOS 9.0 and later and in OS X v10.11 and later, and is available in app extensions.
ATS employs the Transport Layer Security (TLS) protocol version 1.2 (RFC 5246).
The Transport Layer Security (TLS)(A security protocol in common use on the Internet. The successor to SSL) Protocol Version 1.2
http://www.ietf.org/rfc/rfc5246.txt
Fualt
The issue will happen when user try to enroll into MDM with the new 5.2 version of AirWatch Agent App.
At the start of the enrollment, when user try to authenticate either with user email address or server, during the connection, the Handshake is rejected resulting in an error being presented in the application - “An SSL error has occurred and a secure connection to the server cannot be made”.
Existing enrolled device will not be impacted.
We have replicated and confirmed the issue as below
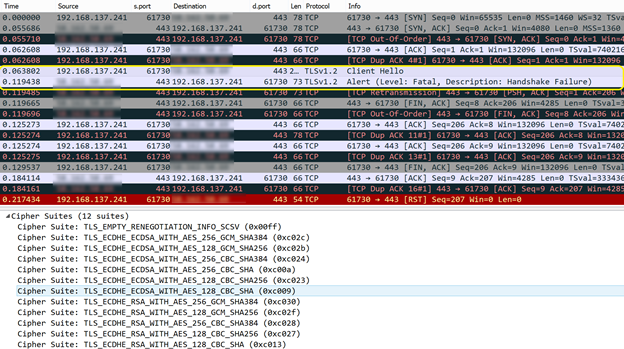
Note: the “Handshake failure” after the “Client Hello”.
We suspect this is due to the update to Apple’s App Transport Security in the App.
We also have particular customer from Australia experiencing this issue, and have escalated to their MDM provider. The MDM provider has now provided a work around on this.
Workaround
Devices are enrolled via Safari browser without using the AirWatch iOS MDM agent (ie the user clicks on a weblink rather than downloading the AW MDM agent).
-
Under Devices and Users>General>Enrollment>Authentication uncheck the “Require Agent Enrollment For iOS" in the AW console
-
Send the default message template to users "DeviceActivation (iOS devices without an AppleID) "
-
The user will receive an email/SMS with a weblink they can use to enroll their iOS device
We are still investigating the root cause of this and will update in future threads, it is however worth checking within your own MDM platform environment even if there are no issue with enrollment. Welcome any input.
.